Data Recovery Service Process
Our data recovery process begins with a free analysis of your hard drive from one of our experienced data recovery technicians in Charlotte. This will take approximately 5-20 minutes of your time and will be conducted while you wait.
No appointment is necessary at our main lab on Independence Blvd. from 6AM-3PM, Monday-Thursday or 6AM-Noon on Fridays; otherwise please call for appointment. We serve clients across the Carolinas, Virginia, Tennessee, and Georgia.
If you prefer, we also have a receiving location in Ballantyne One, 15720 Brixham Hill Avenue, Suite 300, Charlotte, N.C. 28277.
Drives may be dropped off from 9AM-5PM, Monday – Friday and our Charlotte data recovery technicians will have the evaluations complete within 24 hrs.
Based upon the customer description of the failure, in conjunction with visual and electronic tests at our Charlotte facility, our data recovery technician will determine which measures are required to recover your data, estimated time of completion and an exact, upfront, no obligation cost. The quote that you receive will be all inclusive; there will never be any additional charges.
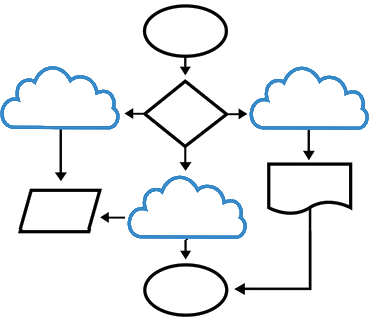
When we receive approval to proceed with the recovery, the diagnostic technician will then assign your hard drive(s) to the appropriate area of our lab:
Physical/hardware issues(clean-room)
Electronic/Firmware issues(electronics lab) and drive imaging, or logical issues to our data reconstruction specialists.
This Charlotte data recovery technician will be a dedicated resource until the recovery is complete and they can answer any questions that you may have throughout the data recovery process.
The final segment of the data recovery process is data verification, copying the data to the media of your choice, and out-processing.
All work is assigned as it is received and we make every attempt to maintain the flow. There are however, times when the flow may be interrupted such as hard drive read issues that can extend the data recovery process significantly or in the case of mission critical recoveries that necessitate completion ASAP.
In the unlikely event that your data is deemed unrecoverable, there will be no charge: No Data – No Fee
Unless requested otherwise, a copy of your data will be retained on our secure servers for 5 business days and then be securely wiped from our system; also at that time we will securely destroy any original data media and dispose of the original housing/parts.
Platforms
Recovery Services
- USB / Memory Cards
- Laptops / Desktops
- External Hard Drives
- Solid State Drives
- RAID/NAS
Secure
- Strict Non-Disclosure
- Chain of Custody Protocol
- High Security Safekeeping
- Confidentiality Agreement
- Controlled Access
- Secure Location